Isn't it interesting how so much attention has been paid to the notion of SM being the father of Jestyn's child Robin and little or no attention paid to just how and under what circumstances Jestyn and SM may have met.
This post sheds a great deal of light on that particular issue and supports the likelihood of it being the case by virtue of a relatively recently released document from British Intelligence dealing with SOE, one time pads and instructresses. Or as SOE puts it, Ciphers, Signals and Sex.
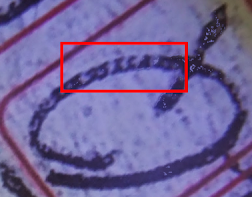
PLEASE NOTE THAT THIS POST HAS BEEN UPDATED WITH SIGNIFICANTLY IMPROVED VIEWS OF VERSE 70 SHOWING MICRO CODE IN DETAIL>
The Real Link Between Alf Boxall and Jestyn
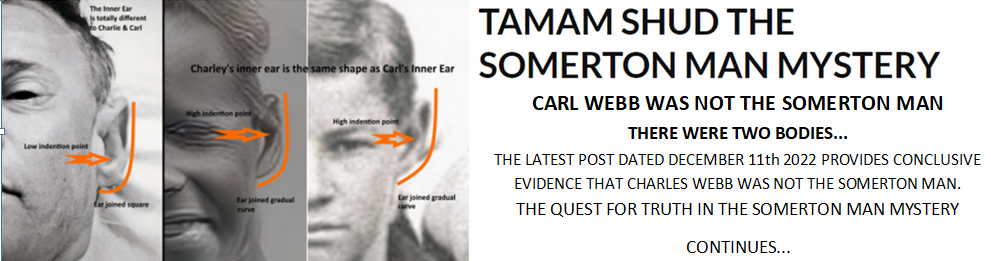
To start this piece, I have been working on the now famous Verse 70 apparently written by Jestyn in a copy of the Rubaiyat of Omar Khayam and handed to him at a meeting held at the Clifton Gardens hotel in 1945. Here is yet more proof of the existence of micro writing only in this case it links Alf Boxall directly to its use and to a clandestine type message.
 |
| The micro examples shown here are real, I have not added anything to them nor have they been subject to any additional marking. |
These images take a while to extract although, in the end, the method needed was simple as always seems to be the case.
The boxes marked 1 and 2 are the number 70 inscribed by Alf Boxall sometime after the Stuart Littlemore interview in 1978.
In box 1.he used some simple letters and numbers as in what appears to HQ 23456 with the 5 and 6 being very close together.
In box 2 you can see traces of letters and numbers but not very clearly as in 1.
Box 3 is I assume by Jestyn. and it looks like 258 8246 with others barely visible.
Box 4. again from Jestyn a string of numbers show up relatively clearly and to me that appears to be 285 395228x
Box 5 is a section of the letter T and I make out 383 46
The process was a simple macro lens close up taken of the high-res image provided by Professor Abbott, I applied a 10 Watt LED oblique light across the surface of the image I then used an image editor to adjust curves.
I belive this to be an example of the British Intelligence, SOE, Ink H method where inked letters are applied which are then overwritten in pencilled micro letters/numbers and a final layer of ink.
My view is that the supposed meeting may not have taken place at the Clifton Gardens Hotel but at Army HQ and it was in fact part of a training exercise.
The Boxall book is still in existence and in my view it is a very real piece of evidence and I would ask you, Professor Abbott to have the book examined by an independent and qualified forensic document examiner. It is highly likely that indentation markings will exist in the book as well as the images I have shown here. With great respect, it is simply not good enough to dismiss the existence of micro writing when you haven't had it tested by a qualified independent examiner.
British Intelligence Involvement in Australia
On the issue of SOE, there is strong evidence that shows that SOE were directly involved with Australia during WW2 by virtue of their distributing various one time pad code material printed on silk. In fact some 366 one time pads were delivered top Australia being sent, here's an excerpt from an SOE document:
VIII. 1944/1945. REAL ADVANCES
1). Agents were now sent into the field with 12 page Letter One Time Pads on silk.
2). W.O.K. or Code 53 on silk.
3). Crack Signal One Time Pad on silk.
4). Broadcast One Time Pad on silk.
5). High Grade Identity Checks.
Consider this, SOE, headed by Leo Marks, had a system in the UK of recruiting Nursing Yeomanry in the code and training section. These ladies were considered exceptional at their work and used the Nursing Yeomanry as a front for their real job. Whilst they may have undertaken some nursing training, they never actually graduated. Interestingly, neither did Jestyn.
Cyphers, Signals and Sex. Instructresses and Agents, A Unique Relationship
The British model also made use of their recruits as instructors to train agents in the use of the various coded materials. In fact they were trained for 15 hours and instructresses were told to make themselves available to the agents as and when required. Read the following section carefully, much is said 'between the lines' in particular note section 6.
XII. TRAINING
To cover this enormous subject would require volumes: it would also require that the reader has at least a working knowledge of the current principles of psycho-analysis – for it was upon certain of these principles that S.O.E.'s cipher training technique was finally evolved.
Briefly, psycho-analysts maintain that (a) behind almost every conscious intention there lingers in the unconscious a deep seated resistance, and (b) Emotion is ambivalent – two sided – what we feel in our conscious mind has its exact opposite in, our unconscious: behind a display of enthusiasm lurks a desire for lethargy – behind a display of affection lurks dislike – behind a display of nausea lurks desire, etc.
The way to discover the existence in the average person of (a) and (b) is through his slips of the tongue, lapse of memory, dreams, gestures, laughter, etc. THIS HOLDS GOOD FOR AGENTS.
The theories of (a) and (b) affect agents in the following ways:-
(1) AGENTS RESENT BEING TRAINED. (This resentment is unconscious).
(2) ENTHUSIASTIC AGENTS DO NOT REALLY WISH TO GO INTO THE FIELD. (This reluctance is unconscious).
(3) AGENTS SEE IN THEIR TRAINING OFFICERS "PARENT IMAGOS" AND REACT ACCORDINGLY. (The fact that the TRAINING OFFICERS are taken as parent imagos is unconscious as far as the agent is concerned, but SHOULD NOT BE as far as the training officers are concerned.
(4) Carelessness, Indolence, Stupidity, or Careless Talk on the part of the agents during training – and indeed afterwards – may be due to UNCONSCIOUS causes.
(5) TRAINING MUST AIM AT THE UNCONSCIOUS OF AN AGENT and not merely to the conscious, otherwise mighty forces may, in the end, bring the most carefully planned training to nought – and an otherwise competent agent may be the despair of his training officer simply because of unconscious trends which no-one has attempted to control.
(6) For further details of the psycho-analytical approach to agents' training, see Appendix entitled "Ciphers, Signals and Sex".
Every agent should go through a post graduate course. It is not enough for an agent to know his ciphers consciously, they must be burned into his unconscious mind so that in moments of acute tension they will be recalled to him with the facility of an instinct.
Constant repetition is imperative. An agent must be told something so often that he begins to react by mimicking his instructor. It is not enough to tell an agent 3 or 4 times about his identity checks, it may not be enough to tell him 30 to 40 times; it is his unconscious mind that must be instructed. Agents should be disturbed at all hours and made to code. Their reactions under intense fatigue should be watched. Paper, spectacles, and electric lights should be removed, and they should be made to improvise methods of coding and decoding traffic. Agents should be grilled before departure to the field. A mock Gestapo session should be set up in which their reactions should be noted. The technique of rebuffing psychological questions should be explained to the agent.
The time it takes to train an agent.
15 hours at a training school.
Post Graduate Course. This consists of every spare second the agent has. Each agent is given his own instructress whose timetable is so arranged that she can be available whenever he requires instruction in cipher. This is a point of psychological importance.
Types of Instructresses. Primarily the extraversive type is best: the dreamy, poetic, aesthetic type was of little use in instructing agents in cipher: the ultra-sophisticated type is even worse. Personable manner, striking or restful appearance are important qualifications for the coding instructress. An agent at a time of intense emotional strain will react far more favourably to a set of characteristics that attract him rather than to the opposite.
Ciphers should be sold to the agent; cipher training is a sales campaign; instructresses should be chosen of the same types as would be used for saleswomen.
A brilliant coder is not necessarily a brilliant instructress in cipher; a brilliant instructress is not necessarily a brilliant coder.
[FINAL PAGE OF REPORT WITHHELD UNDER SECTION 3(4) OF THE PUBLIC RECORDS ACT 1958]
- See more at: http://www.arcre.com/archive/cryptography/cryptosoe#sthash.A9IawyH7.dpuf